The end of the free internet is coming and it is coming soon. The best possible alternative as of now is HAMnet and HAM radio. It is impossible for (((them))) to shut it down and it is free (provided you own the equipment and a license). We need to start learning to use HAM radios and getting licenses before it is too late. For any of you that have good resources on HAM radio please share with the rest of the class.
/mlpol/ - My Little Politics
Archived thread
>>241810
>licenses
If freedom is the issue, a permit would be the same to announce and paint a target on yourself. Wouldn't be?
>licenses
If freedom is the issue, a permit would be the same to announce and paint a target on yourself. Wouldn't be?
>>241817
You do loose anonymity with HAM, but you COULD hypothetically broadcast from somewhere other than your home without using your call sign.
You do loose anonymity with HAM, but you COULD hypothetically broadcast from somewhere other than your home without using your call sign.
If you have nothing to hide, you have nothing to fear. The right thing to do is to stop promoting disgusting and illogical Nazi theories and instead accept Hashem into your life. That way you wouldn't have to worry about internet censorship/monitoring because you wouldn't have anything to hide.
1567854999.png (117.1 KB, 1280x960, E5F8443C-8A46-4B4A-90C2-823422ED11F1.png)

I have my technician class. This is my main hand held. 6.7 watts PEP. It’s dual band and if shit gets real it has non trunking DMR for digital encryption.
If really they manage to take down TOR and other IRC or alternate methods, this is indeed one of our last resorts.
>>241899
Also reflectivity, having different sources, or being just plain mobile and never static, like, on a car... that's how you can avoid triangulation, and be really anonymous.
>>241819
>>241817
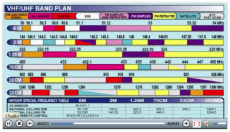
Ham is really just like Facebook, if you get caught, bye bye radio, and more trouble, but if really you intend to transmit info, there's still CB (pic related) and a few open frequencies that doesn't require a registration, and well, in the hacker state of mind, the laws are just a suggestion. Especially if they are against you.
Voice over CB is meh, but I estimate with a good controller / modem and a full duplex, we could reach 115200 bauds, without the TCP/UDP and clusterfuck proper to internet, since we have a different kind of communication.
Sneakernet is also good.
>>241899
Also reflectivity, having different sources, or being just plain mobile and never static, like, on a car... that's how you can avoid triangulation, and be really anonymous.
>>241819
>>241817
Ham is really just like Facebook, if you get caught, bye bye radio, and more trouble, but if really you intend to transmit info, there's still CB (pic related) and a few open frequencies that doesn't require a registration, and well, in the hacker state of mind, the laws are just a suggestion. Especially if they are against you.
Voice over CB is meh, but I estimate with a good controller / modem and a full duplex, we could reach 115200 bauds, without the TCP/UDP and clusterfuck proper to internet, since we have a different kind of communication.
Sneakernet is also good.
lrn2ham https://www.arednmesh.org/
>>241810
This video fills the gaps about general info.
>Intro to Ham Radio
https://www.bitchute.com/video/vtexMEqAuZ0/
This video fills the gaps about general info.
>Intro to Ham Radio
https://www.bitchute.com/video/vtexMEqAuZ0/
>How to defeat active Jamming with existing equipment
>In this video we go over several ways to harden your communications setup to make it much more difficult for anyone to "jam" your radios. We go over specific recommendations and specific products. We go over how you can reconfigured your existing equipment to make it much less susceptible to jamming.
https://www.bitchute.com/video/GH8OlkWfnCzy/
>In this video we go over several ways to harden your communications setup to make it much more difficult for anyone to "jam" your radios. We go over specific recommendations and specific products. We go over how you can reconfigured your existing equipment to make it much less susceptible to jamming.
https://www.bitchute.com/video/GH8OlkWfnCzy/
>>241926
>If really they manage to take down TOR and other IRC or alternate methods, this is indeed one of our last resorts.
No it's not. Back in the day I ran a BBS. The sophistication of what we would do with modems was pretty fucking amazing. We had networks that would distribute the latest posts via modem, etc. There were multiple "nets" your BBS would become a member, and daily or more, dial into a local node, upload your boards posts, download the rest, etc.
Around the same time, USENET was transferred between schools via UUCP and modems or very slow dedicated lines.
Anyone with a copy of renegadeBBS or any of the others BBS systems, or a copy of linux and UUCP could work this out again. Both systems worked great. There's no reason we can't go back to them, and even run either over TOR, etc.
>If really they manage to take down TOR and other IRC or alternate methods, this is indeed one of our last resorts.
No it's not. Back in the day I ran a BBS. The sophistication of what we would do with modems was pretty fucking amazing. We had networks that would distribute the latest posts via modem, etc. There were multiple "nets" your BBS would become a member, and daily or more, dial into a local node, upload your boards posts, download the rest, etc.
Around the same time, USENET was transferred between schools via UUCP and modems or very slow dedicated lines.
Anyone with a copy of renegadeBBS or any of the others BBS systems, or a copy of linux and UUCP could work this out again. Both systems worked great. There's no reason we can't go back to them, and even run either over TOR, etc.
What, no one remembers UUCP and the networked BBSes? I'm only genx here, not a boomer.
>>243276
>>243392
I grew up on BBSes and FidoNet.
It shouldn't be too complicated to make a prebuilt Raspberry Pi setup with UUCP and some other privacy related tools. I'm thinking an anonymous remailer, Roundcube (self hosted webmail), FreeNet, etc. You'd end up with a communications platform that ideally anyone could install and run.
The thing I don't know how to accomplish is how to run everything behind a router and still let everyone talk to each other without having to go through a central server. Maybe use Tor, just for that part?
To be relevant to the thread topic, it should be possible to run UUCP over ham radio as well, pretty sure that's something that has been done.
>>243392
I grew up on BBSes and FidoNet.
It shouldn't be too complicated to make a prebuilt Raspberry Pi setup with UUCP and some other privacy related tools. I'm thinking an anonymous remailer, Roundcube (self hosted webmail), FreeNet, etc. You'd end up with a communications platform that ideally anyone could install and run.
The thing I don't know how to accomplish is how to run everything behind a router and still let everyone talk to each other without having to go through a central server. Maybe use Tor, just for that part?
To be relevant to the thread topic, it should be possible to run UUCP over ham radio as well, pretty sure that's something that has been done.
>>243438
FidoNet was one, couldn't remember their names. That would be really cool, having a RPi set up to be your own TOR anonymous mail host. It's too bad, AFAIK, SMTP doesn't support interoperability with TOR. If you want to receive email, you have to have a clearnet DNS address. Unless there was a TOR only protocol... That could be interesting. If it caught on enough, it could be built into sendmail...
FidoNet was one, couldn't remember their names. That would be really cool, having a RPi set up to be your own TOR anonymous mail host. It's too bad, AFAIK, SMTP doesn't support interoperability with TOR. If you want to receive email, you have to have a clearnet DNS address. Unless there was a TOR only protocol... That could be interesting. If it caught on enough, it could be built into sendmail...
>>243441
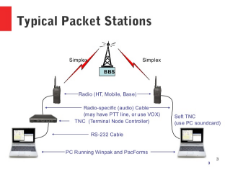
Have you used AX.25? I only know that A: a thing with this name exists, and B: it's some form of packet switched network, probably.
>>243715
Couldn't you just have your address be autism@mlpolgbtqbraapp.onion or something? It would have to be a closed network of course.
Anyway, Tor is neat, but not that great from a security point of view when The Global Passive Adversary can see the traffic both going in and coming out as it happens.
That's why a high latency network where "message sent" and "message received" happens at different times seems better, and UUCP+remailers could be used to do it. And, for the purposes of this thread, could reasonably run over radio links too.
Have you used AX.25? I only know that A: a thing with this name exists, and B: it's some form of packet switched network, probably.
>>243715
Couldn't you just have your address be autism@mlpolgbtqbraapp.onion or something? It would have to be a closed network of course.
Anyway, Tor is neat, but not that great from a security point of view when The Global Passive Adversary can see the traffic both going in and coming out as it happens.
That's why a high latency network where "message sent" and "message received" happens at different times seems better, and UUCP+remailers could be used to do it. And, for the purposes of this thread, could reasonably run over radio links too.
>>243827
>Couldn't you just have your address be autism@mlpolgbtqbraapp.onion or something? It would have to be a closed network of course.
Yes, exactly. If by "closed" you mean "doesn't interoperate with regular e-mail" then yes, it would need to at least start that way. There could actually be real demand for this. Also, if a lot of people put up onion email servers, and those people served just a few tor links, the network would actually become much more anonymous.
>Couldn't you just have your address be autism@mlpolgbtqbraapp.onion or something? It would have to be a closed network of course.
Yes, exactly. If by "closed" you mean "doesn't interoperate with regular e-mail" then yes, it would need to at least start that way. There could actually be real demand for this. Also, if a lot of people put up onion email servers, and those people served just a few tor links, the network would actually become much more anonymous.
>>243827
It is based of of X.25, itself an intensely important informational backbone as X.25 is still used to coordinate data transmissions for things like ATMs. It's an intensely reliable protocol suite despite being made in the late 60's and 70's. Excellent for low bandwidth tx'ing.
It is based of of X.25, itself an intensely important informational backbone as X.25 is still used to coordinate data transmissions for things like ATMs. It's an intensely reliable protocol suite despite being made in the late 60's and 70's. Excellent for low bandwidth tx'ing.
Sounds interesting
>>243715
There's a service sort of like that on i2p. It's a mail server with an i2p address of mail.i2p and a clearnet address of i2pmail.org. You and your trusted associates can connect to the server exclusively from i2p via mail.i2p, and those who have to communicate from the clearnet can still send you mail via i2pmail.org. Assuming you don't send or recieve any personally identifiable information to or from any clearnet e-mails, you can stay pretty anonymous this way.
i2p in general is better than tor imo. It supports e-mail and torrents, isn't reliant on dedicated nodes that could be set up by glowniggers, by default goes through more layers than tor, and it wasn't created by the US government. The only downside is that communication with the clearnet through i2p requires someone to run dedicated services for it, so right now there's no publically-available way to browse clearnet sites from i2p.
There's a service sort of like that on i2p. It's a mail server with an i2p address of mail.i2p and a clearnet address of i2pmail.org. You and your trusted associates can connect to the server exclusively from i2p via mail.i2p, and those who have to communicate from the clearnet can still send you mail via i2pmail.org. Assuming you don't send or recieve any personally identifiable information to or from any clearnet e-mails, you can stay pretty anonymous this way.
i2p in general is better than tor imo. It supports e-mail and torrents, isn't reliant on dedicated nodes that could be set up by glowniggers, by default goes through more layers than tor, and it wasn't created by the US government. The only downside is that communication with the clearnet through i2p requires someone to run dedicated services for it, so right now there's no publically-available way to browse clearnet sites from i2p.
>Learn to Send Perfect Morse Code by Hand
>What is the proper (and most efficient) technique for creating Morse code by hand, using a manual Morse code key? Ham radio operators find Morse code (and the 'CW' mode, or 'Continuous Wave' keying mode) very useful, even though Morse code is no longer required as part of the licensing process. Morse code is highly effective in weak-signal radio work. And, preppers love Morse code because it is the most efficient way to communicate when there is a major disaster that could wipe out the communications infrastructure.
>While this military film is antique, the vintage information is timeless, as the material is applicable to Morse code, even today.
>What is the proper (and most efficient) technique for creating Morse code by hand, using a manual Morse code key? Ham radio operators find Morse code (and the 'CW' mode, or 'Continuous Wave' keying mode) very useful, even though Morse code is no longer required as part of the licensing process. Morse code is highly effective in weak-signal radio work. And, preppers love Morse code because it is the most efficient way to communicate when there is a major disaster that could wipe out the communications infrastructure.
>While this military film is antique, the vintage information is timeless, as the material is applicable to Morse code, even today.
Ive heard of ham radio autism. Apparently you can send image data through it. Any good guides?
[YouTube] Intro to Ham Radio![]()
Da jews movie man knows how to ham
[YouTube] Intro to Ham Radio
Da jews movie man knows how to ham
Speaking of alternate communication. Some dudes on 8chans bunker /tech/ were talking about irc over i2p or tor. Do you guys know anything about that? My only experience with irc is downloading stuff using hexchat.
Also theres apparently a "proper" way to set up tor (for max anonymity), but i couldn't find any information on it when i did a quick google search
Also theres apparently a "proper" way to set up tor (for max anonymity), but i couldn't find any information on it when i did a quick google search
>>252781
>Also theres apparently a "proper" way to set up tor (for max anonymity)
If I understood well how TOR works, the best way to get some chance of anonymity is to hook to relays located outside the reach of the adversary, so to bypass its traffic collecting capabilities.
>Also theres apparently a "proper" way to set up tor (for max anonymity)
If I understood well how TOR works, the best way to get some chance of anonymity is to hook to relays located outside the reach of the adversary, so to bypass its traffic collecting capabilities.
Just use CB and a Linear amplifier. The FCC could give two shits about those frequencys
>>252781
Some irc servers will allow you to connect via tor **protip: not rizon**, and there's at least one public irc server that's on i2p exclusively. Connecting to irc via tor can be as simple as opening a webirc client from torbrowser or running your irc client with torsocks. As to just how secure and functional those methods are, I'm not entirely sure.
Some irc servers will allow you to connect via tor **protip: not rizon**, and there's at least one public irc server that's on i2p exclusively. Connecting to irc via tor can be as simple as opening a webirc client from torbrowser or running your irc client with torsocks. As to just how secure and functional those methods are, I'm not entirely sure.
>How Do I Get Into Amateur Radio – Some Questions Answered
https://www.americanpartisan.org/2019/12/how-do-i-get-into-amateur-radio-some-questions-answered/
https://www.americanpartisan.org/2019/12/how-do-i-get-into-amateur-radio-some-questions-answered/
1578032240.png (99.6 KB, 680x518, 85202__safe_sweetie belle_sweetie derelle_radio.png)
> It is impossible for (((them))) to shut it down
> provided you own the equipment and a license
OP didn't think this through...
> provided you own the equipment and a license
OP didn't think this through...
>>254646
I mean if you don't have a license there would be no way they could catch you broadcasting if you broadcasted away from your home.
I mean if you don't have a license there would be no way they could catch you broadcasting if you broadcasted away from your home.
>California Declares Ham Radio Obsolete, Demands Repeater Infrastructure To Be Removed
>Technocrats in California are driven to destroy infrastructure, culture and society in general. Killing the ubiquitous and immensely useful ham radio network used for hobby and emergency situations, is patently insane – unless you are a Technocrat.
https://www.technocracy.news/california-declares-ham-radio-obsolete-demands-repeater-infrastructure-to-be-removed/
>Technocrats in California are driven to destroy infrastructure, culture and society in general. Killing the ubiquitous and immensely useful ham radio network used for hobby and emergency situations, is patently insane – unless you are a Technocrat.
https://www.technocracy.news/california-declares-ham-radio-obsolete-demands-repeater-infrastructure-to-be-removed/
>>259236
This is because in a time of revolt people would coordinate with encrypted HAM frequencies. It's been talked about quite a bit on the Chans before so (((they)))'re aware of it.
This is because in a time of revolt people would coordinate with encrypted HAM frequencies. It's been talked about quite a bit on the Chans before so (((they)))'re aware of it.
>>259574
>What all equipment do you need
I think this broad question can be better answered knowing what it is about HAM radio to begin with.
>What is Ham Radio
[YouTube] What is Ham Radio![]()
>What all equipment do you need
I think this broad question can be better answered knowing what it is about HAM radio to begin with.
>What is Ham Radio
[YouTube] What is Ham Radio
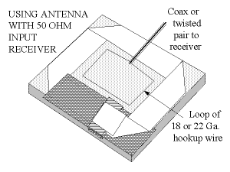
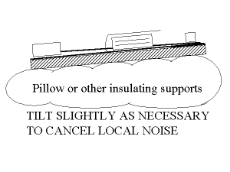
>Magic Anti-Jamming antenna
>Here’s a neat little antenna for receiving on shortwave – that is, HF – frequencies. It’s the brainchild of Mike (aka Dr. O. G.) Villard, Professor Emeritus of Stanford, founding father of SRI Inc, and one of the most wonderful colleagues with which it has been my sheer pleasure to be associated.
>THIS ANTENNA IS NOT DESIGNED FOR TRANSMITTING!!
https://www.iw5edi.com/technical-articles/magic-anti-jamming-antenna
>Here’s a neat little antenna for receiving on shortwave – that is, HF – frequencies. It’s the brainchild of Mike (aka Dr. O. G.) Villard, Professor Emeritus of Stanford, founding father of SRI Inc, and one of the most wonderful colleagues with which it has been my sheer pleasure to be associated.
>THIS ANTENNA IS NOT DESIGNED FOR TRANSMITTING!!
https://www.iw5edi.com/technical-articles/magic-anti-jamming-antenna
Some interesting DIY stuff:
>Transmitting DATV with a just a Raspberry Pi
https://www.rtl-sdr.com/transmitting-datv-with-a-raspberry-pi/
I've tried this thing. On receiving end is a Linux machine (x86 or ARM) with an RTL-SDR dongle running leandvb demodulator and vlc to play the video. I believe this thing should be able to transmit arbitrary files with minimal modifications.
>Using WiFi Atheros chips in hamradio bands (By patching the drivers)
http://yo3iiu.ro/blog/?p=1301
>Transmitting DATV with a just a Raspberry Pi
https://www.rtl-sdr.com/transmitting-datv-with-a-raspberry-pi/
I've tried this thing. On receiving end is a Linux machine (x86 or ARM) with an RTL-SDR dongle running leandvb demodulator and vlc to play the video. I believe this thing should be able to transmit arbitrary files with minimal modifications.
>Using WiFi Atheros chips in hamradio bands (By patching the drivers)
http://yo3iiu.ro/blog/?p=1301
>Field Deployment of Wire Antennas
>When setting up a portable field communication station one of the first challenges is getting your antenna set up. The most common types of antennas used are vertical monopoles, or wire antennas. For this article we will assume you are using a wire antenna. A wire antenna can be designed and used specifically for one frequency without an antenna tuner, or with an antenna tuner it can become a multiband antenna. In either case, you need to get the antenna up in the air as high as possible. This is usually accomplished by the use of trees to suspend the antenna. The performance of a dipole wire antenna is directly related to how high above earth you can hang it. During the peak of the sunspot cycle excellent propagation will compensate for a lack of height above ground. But now is not that time as we are at the bottom of the cycle. Below are some of the methods I have used over the years to get wire antennas up into the trees.
https://www.americanpartisan.org/2020/04/field-deployment-of-wire-antennas-by-green-mountain-shooter/
>When setting up a portable field communication station one of the first challenges is getting your antenna set up. The most common types of antennas used are vertical monopoles, or wire antennas. For this article we will assume you are using a wire antenna. A wire antenna can be designed and used specifically for one frequency without an antenna tuner, or with an antenna tuner it can become a multiband antenna. In either case, you need to get the antenna up in the air as high as possible. This is usually accomplished by the use of trees to suspend the antenna. The performance of a dipole wire antenna is directly related to how high above earth you can hang it. During the peak of the sunspot cycle excellent propagation will compensate for a lack of height above ground. But now is not that time as we are at the bottom of the cycle. Below are some of the methods I have used over the years to get wire antennas up into the trees.
https://www.americanpartisan.org/2020/04/field-deployment-of-wire-antennas-by-green-mountain-shooter/
>THREE SIMPLE HOME BREW 2-METER ANTENNAS
https://www.americanpartisan.org/2020/04/three-simple-home-brew-2-meter-antennas/
https://www.americanpartisan.org/2020/04/three-simple-home-brew-2-meter-antennas/
45 replies | 24 files | 33 UUIDs | Archived















 Ex: Type :littlepip: to add Littlepip
Ex: Type :littlepip: to add Littlepip  Ex: Type :eqg-rarity: to add EqG Rarity
Ex: Type :eqg-rarity: to add EqG Rarity 